Recruitment - CSCG 2025 - Write-Up
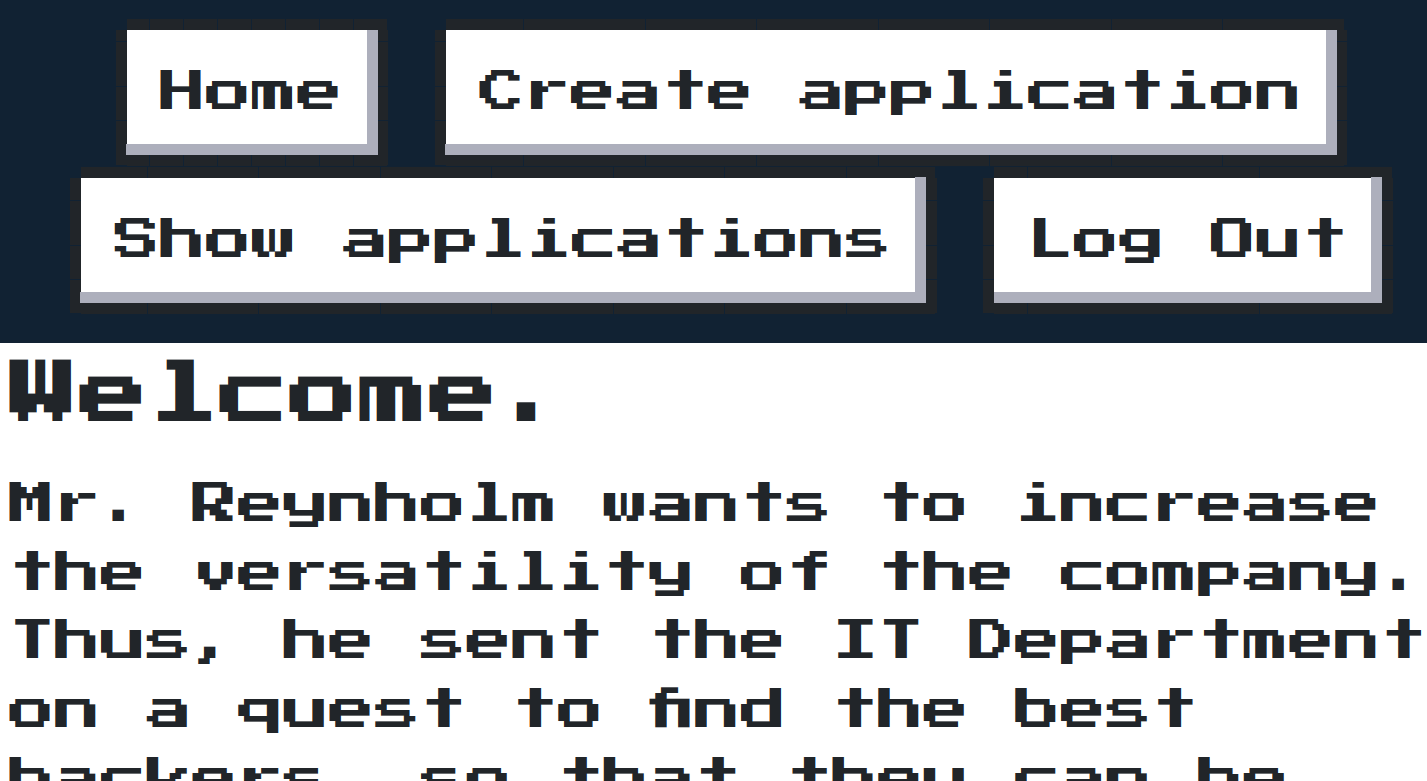
Exploit a XSS vulnerability.
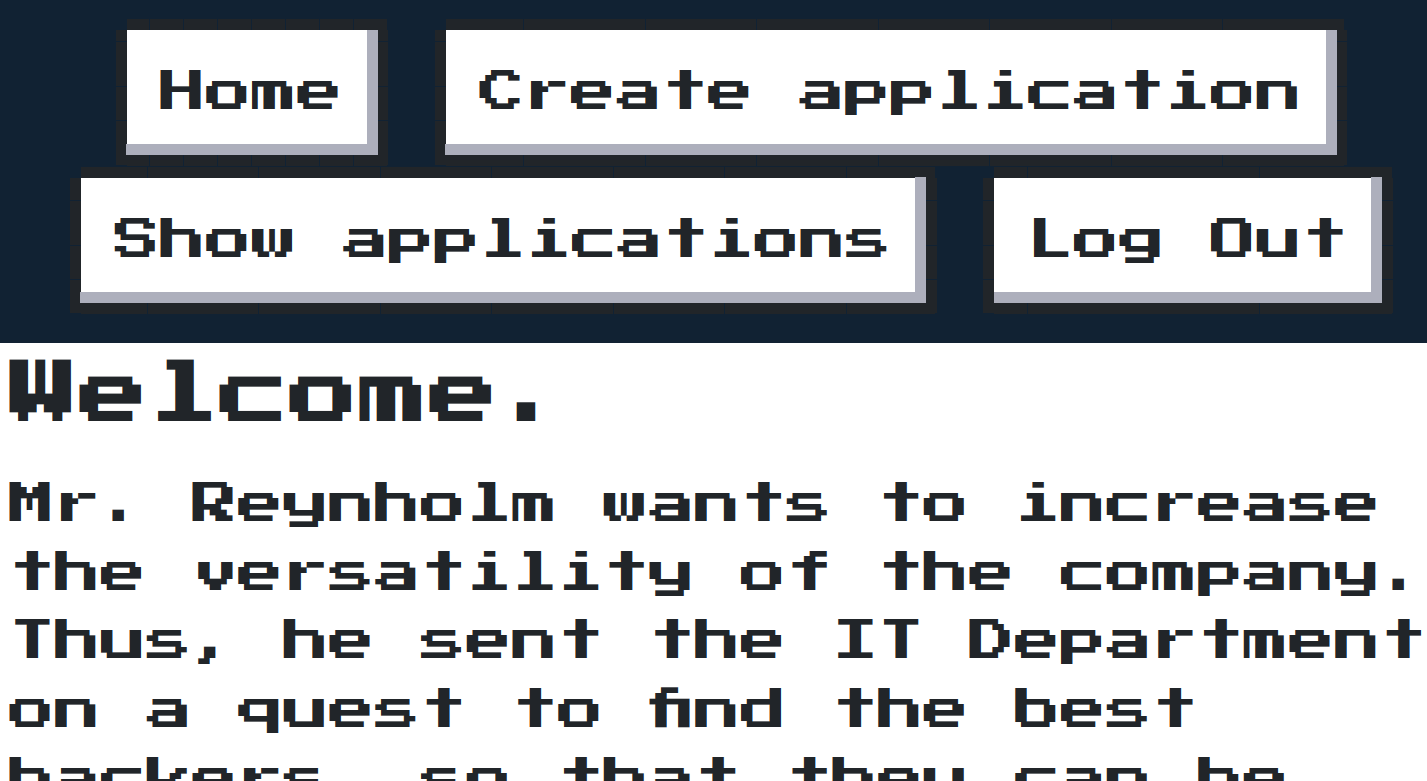
Exploit a XSS vulnerability.
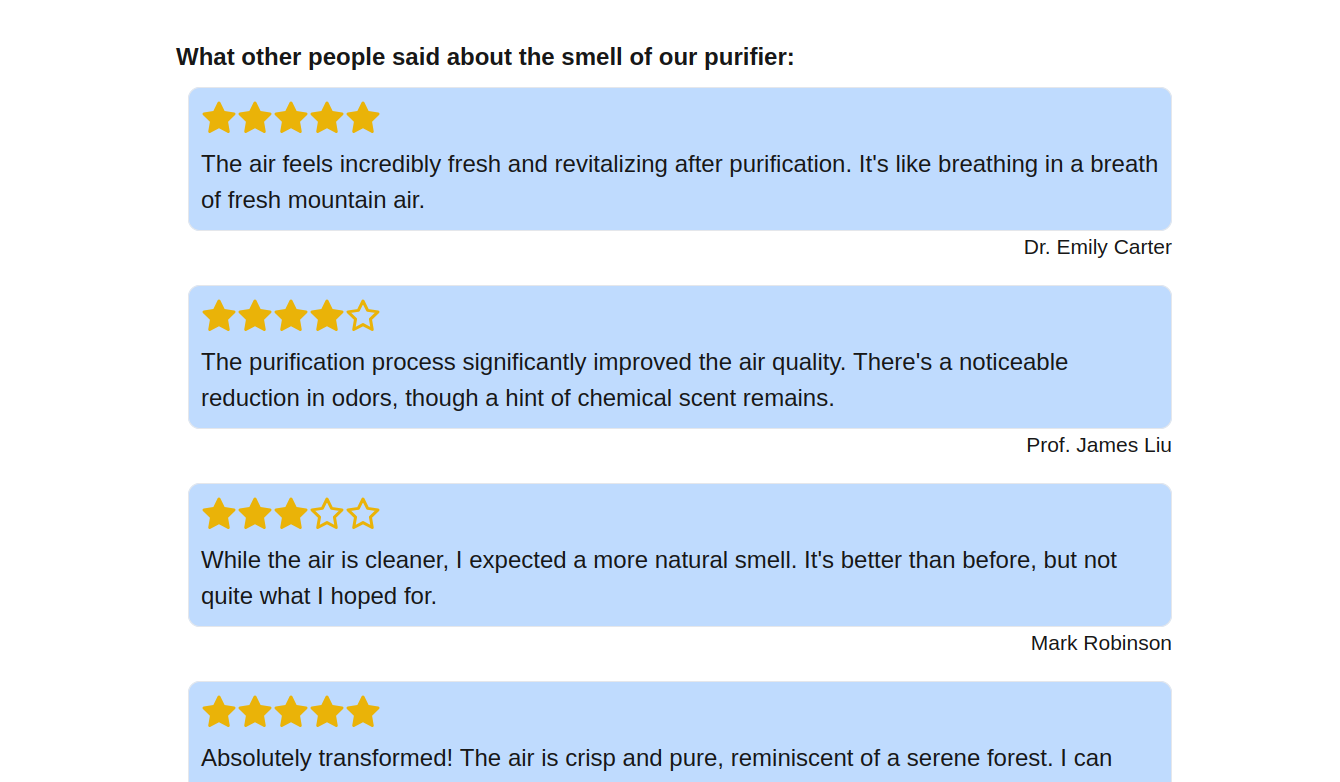
Find a XSS vulnerability.
Find a Information Disclosure vulnerability.
Escalate your privileges with kubernetes.
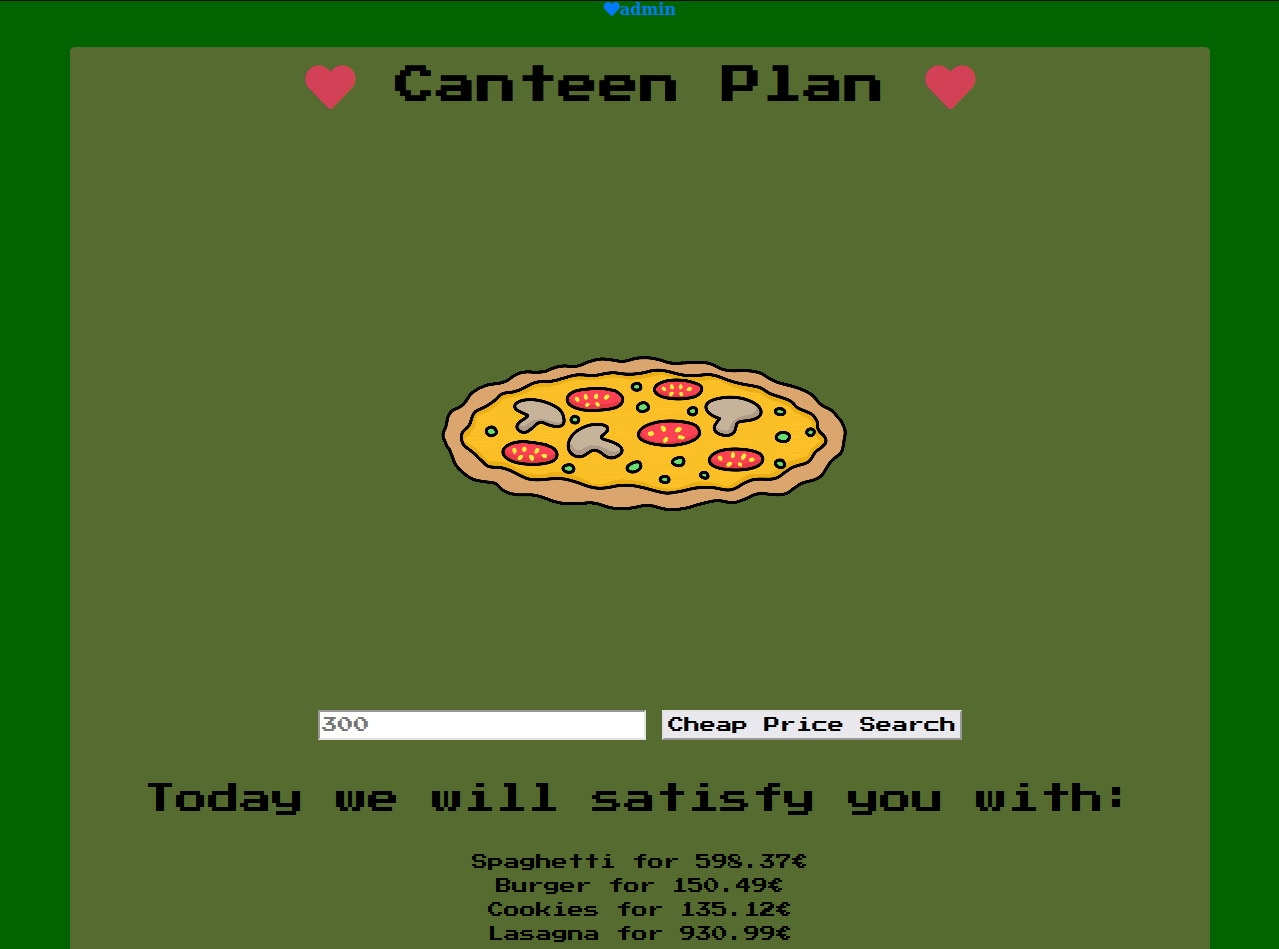
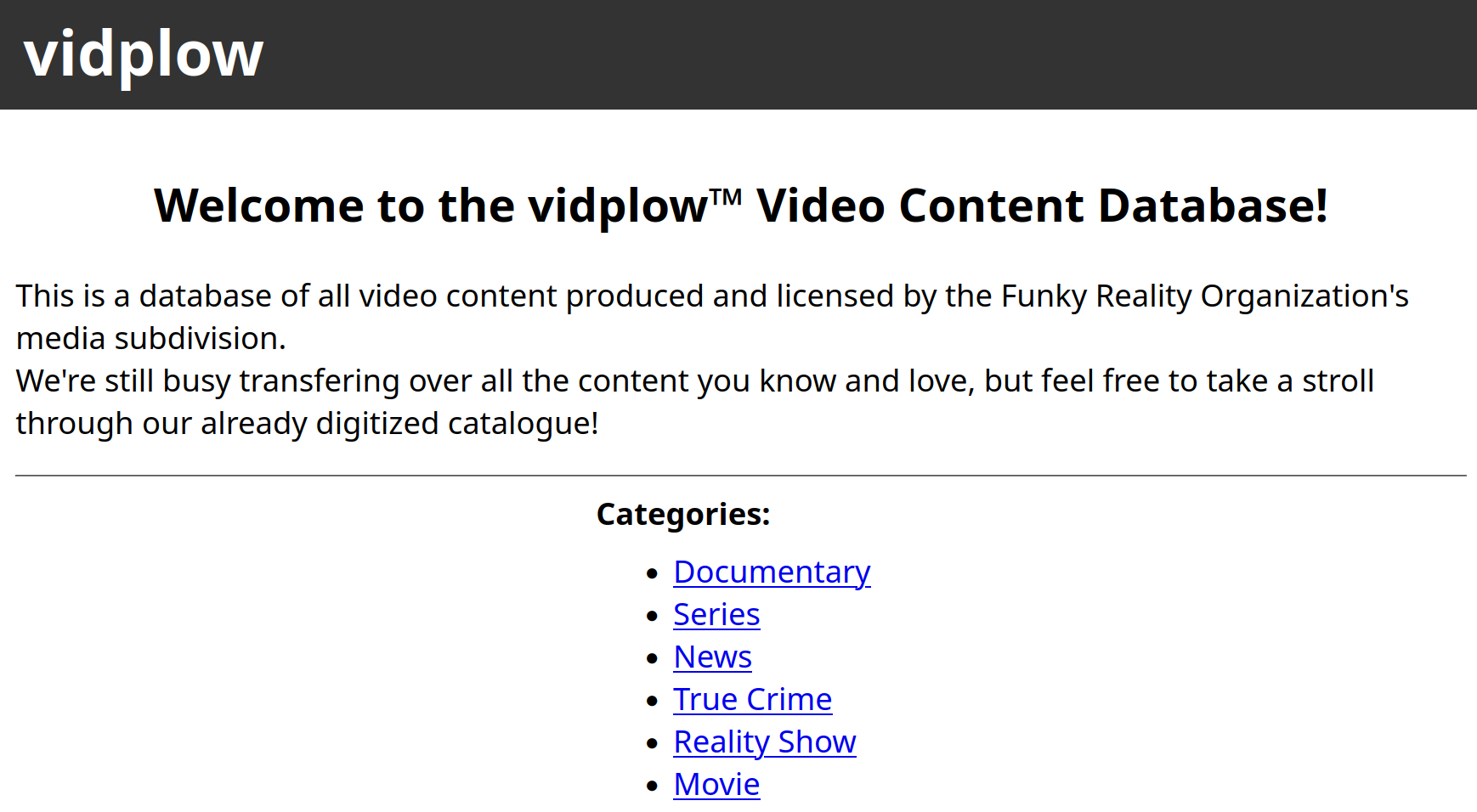
Find a SQL injection vulnerability and a insecure object deserialization vulnerability to get the flag.

Escalate your privileges with kubernetes.

Investigate traffic of a C2 connection.

Use a AES-CRT padding oracle vulnerability to extract the flag.

Leak data and solve a sudoku.
Break a weak RSA cookie encryption system and retrieve the flag.